Blockchain Attack Vectors: Risks & Impact
Explore Blockchain Attack Vectors: 51% Attack, Sybil Attack, Eclipse Attack, DDoS, Smart Contract Weaknesses, and Timejacking. Protect Your Blockchain Network.

As 2023 approaches, it is time to plan the next year budget of the company, and cybersecurity spending must be prioritized. The budgeting procedure must also evolve to keep up with the rapid technological changes. When deciding how to spend company’s cybersecurity budget in 2023, keep in mind that the end goal is not to buy more tools to keep chasing the ever-increasing number of vulnerabilities; it is to develop a plan and budget that minimizes your company’s exposure to risk and the damage that security breaches could cause.
What should your Cybersecurity budget include in 2023? The answer to this question and other important considerations are listed in this article.
Since it varies by company and sector, there is no universally applicable amount or percentage of funds to allocate to cybersecurity. You cannot protect until you have not identified your needs for protection.
Understanding your company’s current status and assets is critical to effective budget lane planning. An inventory of current assets, such as physical, virtual, SaaS, sensitive data, and others are the first step for planning the cybersecurity budget. This will save money and time and clear any confusion about your company’s responsibilities. 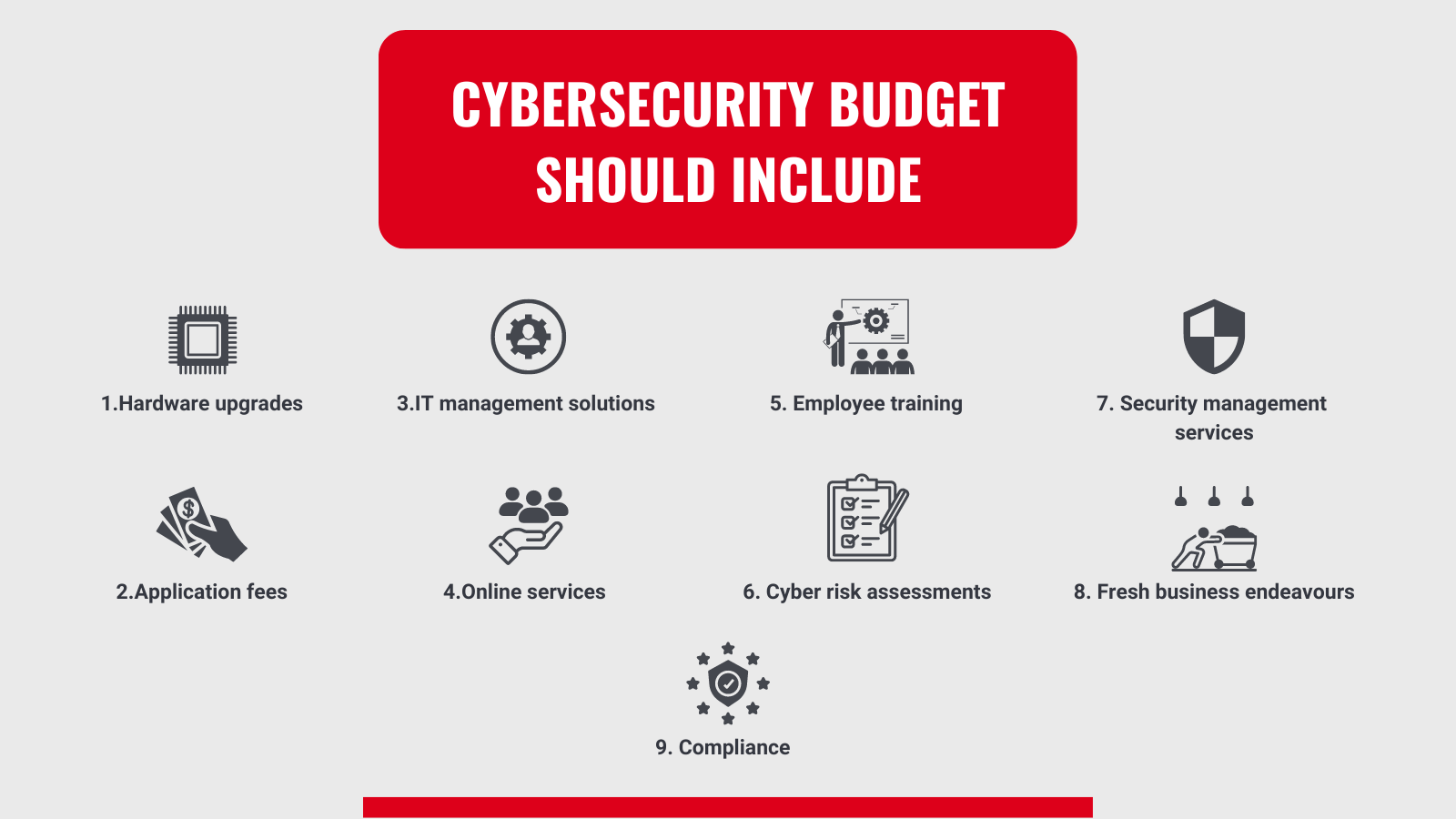
Four different budgeting approaches are available for companies looking to adopt cybersecurity plans.
In a reactive approach, action is taken only when an unexpected problem arises. While all three components—prevention, detection, and response—should be accounted for in a comprehensive cybersecurity budget, most companies place more emphasis on prevention.
Since the proactive approach to cybersecurity requires considering the full strategy (detection, prevention, and response), budgeting is founded on a thorough understanding of the entire process. In addition, IT experts would add the expenses of conducting regular cyber security tests like vulnerability assessments and pen-tests yearly.
It includes studying the cybersecurity strategies of other organizations, including their organizational structure, level of investment in security, key performance indicators (KPIs), and others, to secure a relevant budget to provide an effective defence.
Risk-based Approach assigns various levels of danger to different parts of the company's security lifecycle. Organizations that have reached a certain level of maturity in terms of security will benefit from this method because of their ability to classify risks across domains and allocate resources accordingly.
The complexity of cybercrime means it is always changing, and the pace of evolution will quicken as new forms of malware, such as ransomware, appear. Adopting IoT increases endpoints, which increases cybersecurity costs due to the number of vulnerabilities that must be protected against.
Such vulnerabilities include weak passwords, unpatched servers, leaked critical information like login details, and compromised assets like fake website domains and the company’s mobile app.
Microsoft predicts that by 2025, a shortage of 3.5 million people will exist in the field of cybersecurity. It is not an easy job because no matter how advanced a company’s cybersecurity procedures are, IT professionals will always be needed to watch the network and respond quickly if something goes wrong.
Therefore, CISOs must adopt novel recruitment strategies and fortify their organizations to cope with the resulting skills shortage. In addition, to using outsourced security services, a good first step would be to train team members.
Since most cybercrimes are committed for financial gain, the state of the global economy will influence their frequency. The global economy is projected to contract by 2.9% in 2022. This trend is expected to continue through 2023 and 2024, creating an opening for cybercriminals even as it causes stress to millions of people.
During a recession, fraud is the most common cybersecurity attack, so extra money needs to be spent on identity-based access controls and other methods of protecting sensitive financial and personal data.
Increased cybercrime calls for increased spending on cybersecurity measures, which is typically what happens when major geopolitical events occur. Due to the interconnected nature of the modern internet, events that take place economically or politically on the other side of the world will impact businesses thousands of miles away.
Therefore, it is crucial to be ready for such incidents. One of the most common attacks in such cases is ransomware to extort money and protest the geopolitical event in question.
Cybersecurity is a rapidly developing field, so laws enacted to protect personal information are frequently revised to keep up. When an organization has implemented adequate security measures, the cost of achieving and maintaining compliance should drop. This is crucial in light of the ever-increasing expense of adhering to a wide range of privacy regulations and contractual security obligations.
Adopting the Zero Trust approach with a first-rate user experience reduces the likelihood of an incident. It boosts confidence and the capacity to enhance an organization’s overall security posture, making it the ideal replacement for the outdated practice of relying solely on physical barriers to keep out cybercriminals. In this type of approach, the prevention is the focus of the Zero Trust security model rather than detection and remediation. Models of security based on zero trust ensure that users and devices are subject to constant authorization and verification. Most attacks rely on taking advantage of soft spots, like careless users or poorly chosen passwords, which could be crucial.
As with anything else, it is better to be safe than sorry. Spend as much as you want on cyber protection, but if you do not have a plan in place for dealing with emergencies, you could be in serious trouble. Verify that the level of risk outlined in your most recent risk assessments is reflected in the coverage and support provided by your response plan.
Cybersecurity is an important and one of the most expensive areas of nowadays company’s budget in today’s business world. As a result, careful planning is required to ensure complete coverage and protection. At the same time, cybersecurity varies from company to company. Some major factors, such as economic conditions, conflicts, and regulations, result in major cyberattacks that must be considered during the next year’s budget planning.